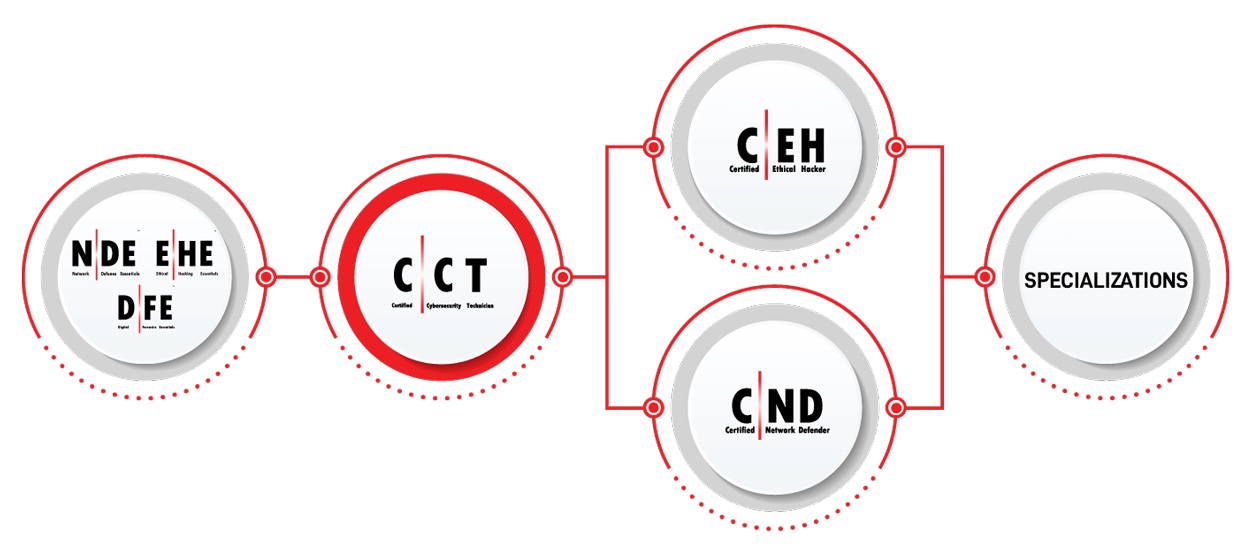
Certified Cybersecurity Technician (C|CT)
Learning Objectives

Key issues plaguing the cybersecurity industry (information security and network security)
Information security threats, vulnerabilities, and attacks

Different types of malware
Network security fundamentals

Identification, authentication, and authorization concepts
Network security controls
Network security assessment techniques and tools
Application security design and testing techniques
- Fundamentals of virtualization, cloud computing, and cloud security
- Wireless network fundamentals, wireless encryption, and security measures
- Fundamentals of mobile, IoT, and OT devices and their security measures
- Cryptography and public key infrastructure concepts
- Data security controls, data backup and retention methods, and data loss prevention techniques
- Network troubleshooting, traffic monitoring, log monitoring, and analysis for suspicious traffic
- Incident handling and response process
- Computer forensics fundaments, digital evidence, and forensic investigation phases
- Download Course PDF
Course Schedule

SESSION 1:
- Information Security Threats and Vulnerabilities
- Information Security Attacks
- Network Security Fundamentals
- Identification, Authentication, and Authorization
SESSION 2:
- Network Security Controls – Administrative Controls
- Network Security Controls – Physical Controls
- Network Security Controls – Technical Controls
- Network Security Assessment Techniques and Tools
SESSION 3:
- Application Security
- Virtualization and Cloud Computing
- Wireless Network Security
- Mobile Device Security
SESSION 4:
- IoT and OT Security
- Cryptography
- Data Security
- Network Troubleshooting
- Network Traffic Monitoring
SESSION 5:
- Network Logs Monitoring and Analysis
- Incident Response
- Computer Forensics
- Business Continuity and Disaster Recovery
- Risk Management

Training program
How Will the Certified Cybersecurity Technician Credential Benefit You?
It facilitates your entry into the cybersecurity realm as a cybersecurity technician. It provides fundamental professional skills and solidifies the concepts of information security, network security, computer forensics, risk management, and incident handling.
It enhances your skills as a cybersecurity specialist and increases your employability chances. It provides hands-on practical skills essential for a cybersecurity technician or any role in IT with administrative privileges where security should be considered and practiced.

Students will learn:
- To validate hands-on technician level IT and cybersecurity skills.
- It’s an entry-level cybersecurity program engineered by the creators of the Certified Ethical Hacker program to address the global demand for cybersecurity technicians.
- To prepare individuals with core security skills to pursue and develop their cybersecurity careers as cybersecurity specialists, consultants, network engineers, or IT administrators

C|CT’s Key Offerings:
Strong Foundational Coverage
The C|CT certification provides total foundational cybersecurity domain coverage with key concepts in each domain combined with practical hands-on labs and critical thinking challenges producing world-class cyber security technologists.
Live Range Experience
Other popular programs rely on simulation and interactivity as practical-based assessment, the C|CT program is delivered on a live Cyber Range utilizing live targets and real attack systems for a truly immersive, real-life practice and assessment platform.
Capture the Flag
The C|CT certification offers capture the flag (CTF) style critical thinking challenges to accompany each lab exercise putting knowledge into practice and providing a proven record of skill demonstration. Candidates completing the C|CT program will earn the C|CT certification and have a proven track record of performing the tasks required in a live Cyber Range, proving to employers their ability to perform critical job duties.
Multiple Certifications
The course outline of the C|CT program goes above and beyond some of the more common entry-level cybersecurity programs, such as the Security+, in a completely hands-on cyber range environment instead of simulations to ensure cybersecurity skills development. We believe that candidates who successfully attain the C|CT certification will attain other leading cybersecurity certifications, including Security+, without further training
Most Affordable
Despite the unique design of the heavily hands-on course and its uses of real-world cyber range capability, the certification is one of the most affordable in the world!

Register For Class
Date |
Type |
Location |
|---|
NOT SURE WHERE TO START?
Private Team Training
Enrolling at least 3 people in this course? Consider bringing this (or any course that can be custom designed) to your preferred location as a private team training
For details, call 704-554-3827

Come Learn With Intellectual Point
Price Match Guarantee!
We will match Competitor’s Price Quote.
Call for more details 703-554-3827
A Certified Certified Cybersecurity Technician (C|CT) Course at Intellectual Point Includes:
-
Live instructor-led training in modern classrooms
-
Thorough review of all EC-Council Certified Cybersecurity Technician (C|CT) topics by industry experts
-
Hands-on labs on real CCT technologies
-
24 x 7 access to the real labs in classrooms and remotely
-
100% latest material & and realistic practice questions
-
Confidence building hands-on training
-
Authorized Pearson VUE testing at the same location to help you complete your exam*
-
Study material, notes, videos, and practice questions included in the course price
happy clients
What Our Customers Say - Based on over 600+ Reviews!