
A Simple Guide In Landing Your Ideal Cybersecurity Position
Have the right mindset when starting your career in cybersecurity
Be determined by having set goals on how far you want to take your IT career. Other stronger candidates will be always present, it is your job to not let that phase you. The most important trait to possess is the willingness to learn and be coachable when advancing in your cloud computing journey.
After completing certifications an individual must:
- Keep practicing often after obtaining certifications.
- Keep learning more from peers.
- Keep looking for ways to advance in your career by opening more interview opportunities.

Foundation to Intermediate Skills
Good foundational certifications are:
You must learn the basics of Networking and a strong foundation on Linux. From there, students can expand and learn Splunk, or cloud security certifications depending on what track they want to pursue.

It should be a goal to first work in a Security Operations Center (SOC) as an operation analyst. Operations work alongside security engineers and SOC managers. As a group, their role encompasses “providing situational awareness through the detection, containment, and remediation of IT threats.” The group monitors any cyber-attacks and determines if it a threat or malicious.
Candidates for the SOC analyst position must have analytical skills, communication skills, and the desire to stay up-to-date on the latest technology. It’s also important that you are prepared to sift through huge amounts of information to identify threats or other security issues, and to be flexible and available at any time – because threats and attacks can happen at any time, day or night.
Students can then move on to Certified Ethical Hacker (CEH) Training Courses at the intermediate level. They can learn the fundamentals of footprinting, network scanning, system hacking, sniffing, session hijacking, web servers, and web application hacking.

Entry-level positions include:
- Cybersecurity Specialist/ Technician – Cybersecurity specialists play a key role in monitoring, detecting, investigating, analyzing, and responding to security events, cybersecurity specialists protect systems from cybersecurity risks, threats, and vulnerabilities.
- Cyber Crime Analyst/ Investigator – Cybercrime analysts and investigators require an understanding of how malware compromises a system and the methodologies behind digital forensics, including identifying, preserving, extracting, analyzing and reporting on cybercrime evidence.
- Incident Analyst/Responder – working to monitor and report current networks/systems and examining security practices and procedures to find areas for operational improvement.
- IT Auditor – They report problems related to IT systems, analyze data and increase internal controls. Much of their work time is spent collecting and reviewing data from databases, software programs, and information management systems.

Mid-level positions include:
- Cybersecurity Analyst – evaluate, plan and implement the security systems that protect an organization’s IT infrastructure and data; this includes the safeguarding of digital assets by responding to incidents like viruses and breaches, reviewing suspicious activity and concentrating on the discovery of vulnerabilities. They also investigate alerts and implement threat protection measures and security controls.
- Cybersecurity Consultant – When an organization’s budget or need does not warrant full-time information security staff, they hire a cybersecurity consultant. They are usually their own boss and work on a fixed contract to resolve security issues.
- Penetration & Vulnerability Tester – Penetration and vulnerability testers require a thorough understanding of pentesting methodologies and vulnerability assessments, as well as the ability to exploit systems and effectively communicate findings.

Advanced Positions include:
- Cybersecurity Manager / Administrator – they require an advanced understanding of information security concepts, security operations, and information assurance, as well as risk management and project management skills.
- Cybersecurity Engineer – A cybersecurity engineer is an information security professional that performs many functions including designing, developing and implementing secure network solutions to defend against advanced cyberattacks, hacking and persistent threats.
- Cybersecurity Architect – A Security Architect designs, builds and oversees the implementation of network and computer security for an organization. As a senior-level employee, you’ll be responsible for creating complex security structures – and ensuring that they work. In addition to handling defense (e.g. vulnerability testing, installing firewalls, etc.) and response (e.g. dealing with security-related incidents), you’ll often be building security infrastructures, providing technical guidance, assessing costs & risks, and establishing security policies and procedures.

Focus on the Tools Used By Cybersecurity Specialists
Know the tools and get familiarized with what they do. Pick one tool and master it so that you can be employable in the marketplace.
Mitre Att&ck Framework – ATT&CK stands for adversarial tactics, techniques, and common knowledge. The ATT&CK knowledge base is used as a foundation for the development of specific threat models and methodologies in the private sector, in government, and in the cybersecurity product and service community.
Splunk – fastest growing and most popular tool. It is a software platform to search, analyze and visualize the machine-generated data gathered from the websites, applications, sensors, devices, etc. which make up your IT infrastructure and business.
Tenable / Nessus – tool used by the Federal Government. Nessus is a proprietary vulnerability scanner developed by Tenable
Other tools include:
PaloAlto Networks, OpenVas, Elastic, Logstash, NMAP

Use Intellectual Point’s Resources
This rapid test prep trains you in the certification and in real-world problems. It also simulates what happens in the real world, and students can take certain steps to block the cyberattack. Please visit our Rapid Test Prep Resource section for details.
Ask one of Intellectual Point’s IT mentors to help you in your career path. It all depends on what areas you are good at and what you want to pursue.
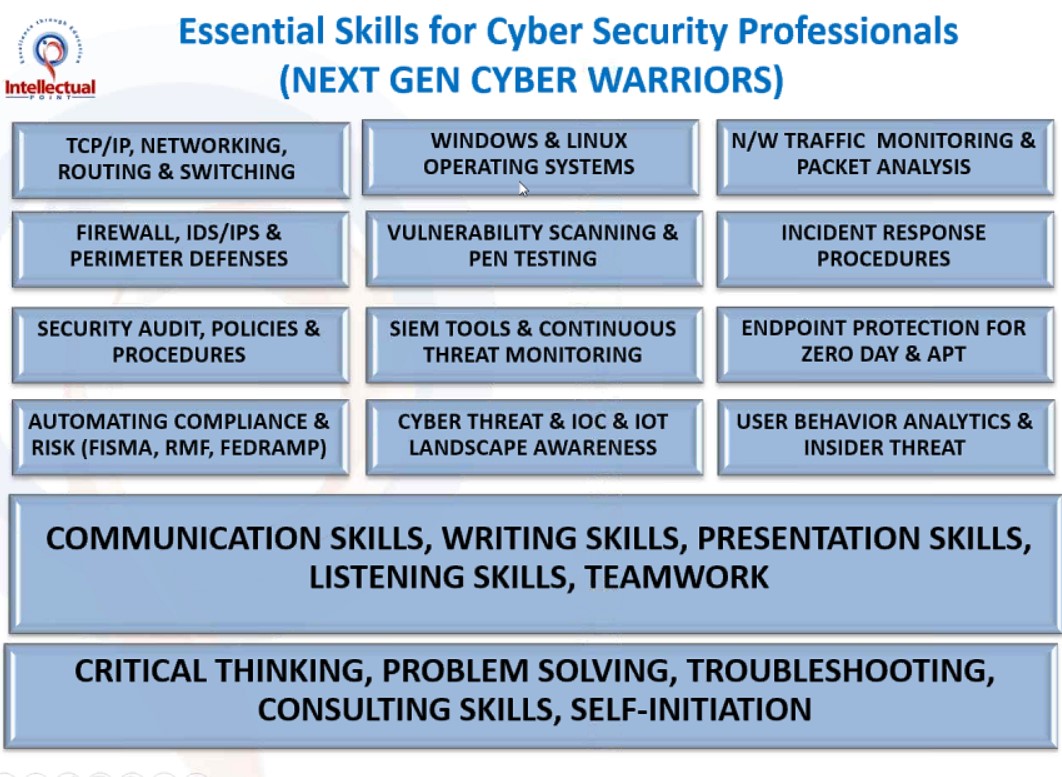
Practice your soft and hard skills
Understand business goals and align them with real analytics and KPIs. It is not simply about the knowledge base, the manager is looking to see if you can work in teams, analyze information, and how you can investigate cyberattacks. It is beneficial for students to improve their communication skills, writing skills, presentation skills, and listening skills when advancing their IT career. Nowadays it is all about teamwork and collaboration to accomplish a task
The student also much takes initiation in learning how to problem-solve complex tasks by thinking critically about the problem. This way the student can troubleshoot the problem and come to a reasonable solution. It is important to think outside the box and ask the right questions to get to the problem once you investigate a cyberattack.






























